Manufacturing is now the most targeted industry for cyberattacks worldwide. According to IBM's X-Force Threat Intelligence Index, manufacturing has held the top spot for ransomware and extortion attacks for several consecutive years, surpassing even financial services and healthcare. The reason is straightforward: manufacturers cannot afford downtime, making them prime targets for threat actors who know a disrupted production line translates directly into lost revenue, missed contracts, and supply chain failures.
See also: penetration testing for government contractors. For more context, see cmmc penetration testing and cloud penetration testing.Despite this threat landscape, many manufacturing organizations still treat cybersecurity as an IT-only concern. Operational technology (OT) networks, programmable logic controllers (PLCs), human-machine interfaces (HMIs), and industrial control systems (ICS) often operate with minimal security oversight. Penetration testing specifically designed for manufacturing environments bridges this gap by identifying exploitable vulnerabilities across both IT and OT domains before attackers can leverage them.
Why Manufacturing Is a Prime Target
Several factors make manufacturing uniquely vulnerable to cyber threats. First, the industry relies heavily on legacy systems. Many production environments run equipment with 15- to 20-year lifecycles, often using outdated operating systems like Windows XP or proprietary firmware that no longer receives security patches. These systems were designed for reliability and uptime, not security, and they were never intended to be connected to the internet.
Second, the convergence of IT and OT networks has dramatically expanded the attack surface. Industry 4.0 initiatives, smart factory deployments, and Industrial Internet of Things (IIoT) sensors have connected previously air-gapped OT environments to corporate networks and cloud platforms. While this connectivity drives efficiency and data-driven decision making, it also creates pathways that attackers can exploit to pivot from a compromised email account directly into production control systems.
Third, manufacturing supply chains are deeply interconnected. A single manufacturer may have dozens of vendors, contractors, and partners with some level of network access. Each of these connections represents a potential entry point. The consequences of a breach extend beyond data theft: attackers who gain control of industrial processes can cause physical damage to equipment, compromise product quality, or create safety hazards for workers.
What Manufacturing Penetration Testing Covers
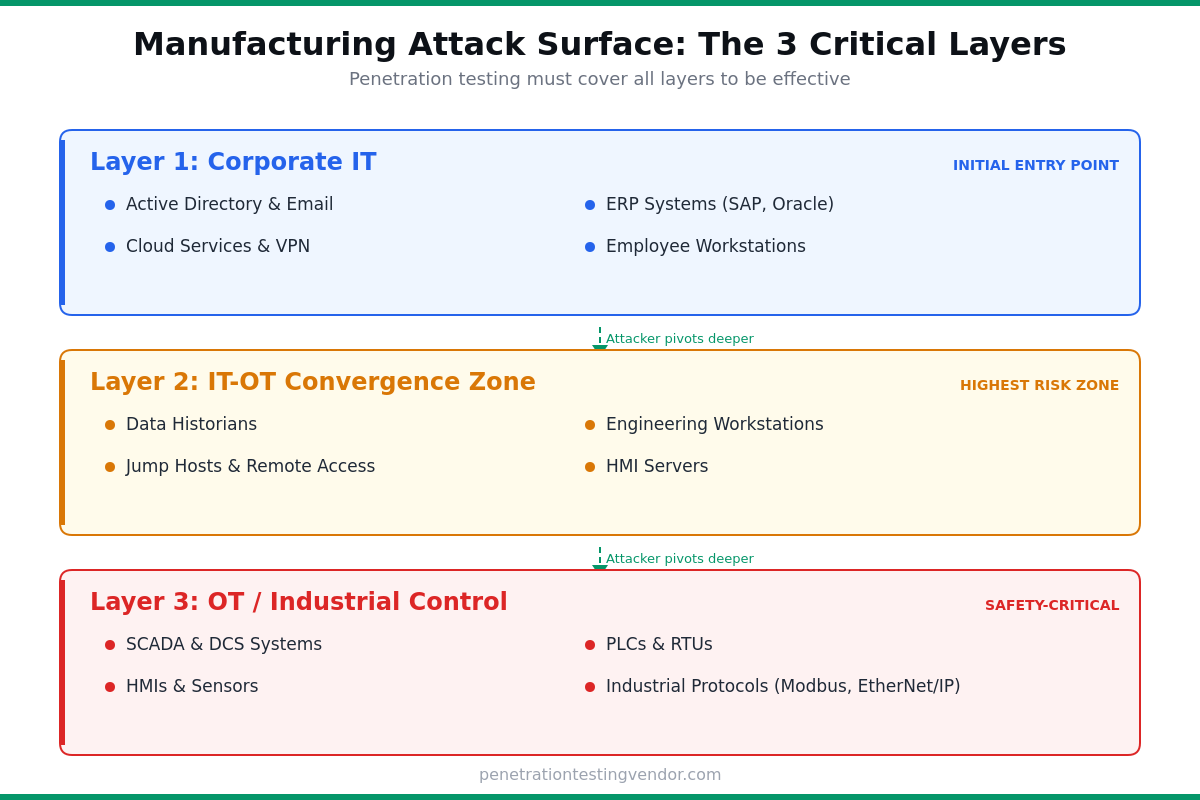
A comprehensive penetration test for a manufacturing organization should address multiple layers of the technology stack. Unlike a standard corporate pen test that focuses primarily on web applications and network infrastructure, manufacturing engagements must account for the unique protocols, devices, and safety considerations present in industrial environments.
The IT infrastructure layer includes the corporate network, Active Directory environment, email systems, ERP platforms (such as SAP or Oracle), and any cloud services. Testers assess these components using standard enterprise penetration testing techniques, looking for misconfigurations, unpatched vulnerabilities, weak credentials, and privilege escalation paths. This layer matters because it is typically the initial entry point for attackers who then pivot toward OT systems.
The OT and ICS layer encompasses SCADA systems, PLCs, HMIs, distributed control systems (DCS), and the industrial protocols that connect them. Common protocols found in manufacturing include Modbus, EtherNet/IP, OPC UA, PROFINET, and BACnet. Penetration testers with OT expertise assess whether these systems are properly segmented from the corporate network, whether default credentials have been changed, and whether unauthorized commands can be sent to controllers. This testing must be performed carefully to avoid disrupting active production processes.
The IT-OT convergence zone is where most critical vulnerabilities are found. This includes jump hosts, data historians, engineering workstations, and remote access solutions that bridge the gap between corporate IT and the production floor. Attackers frequently target these convergence points because compromising a single data historian or engineering workstation can provide access to both domains.
Key Vulnerabilities Found in Manufacturing Environments
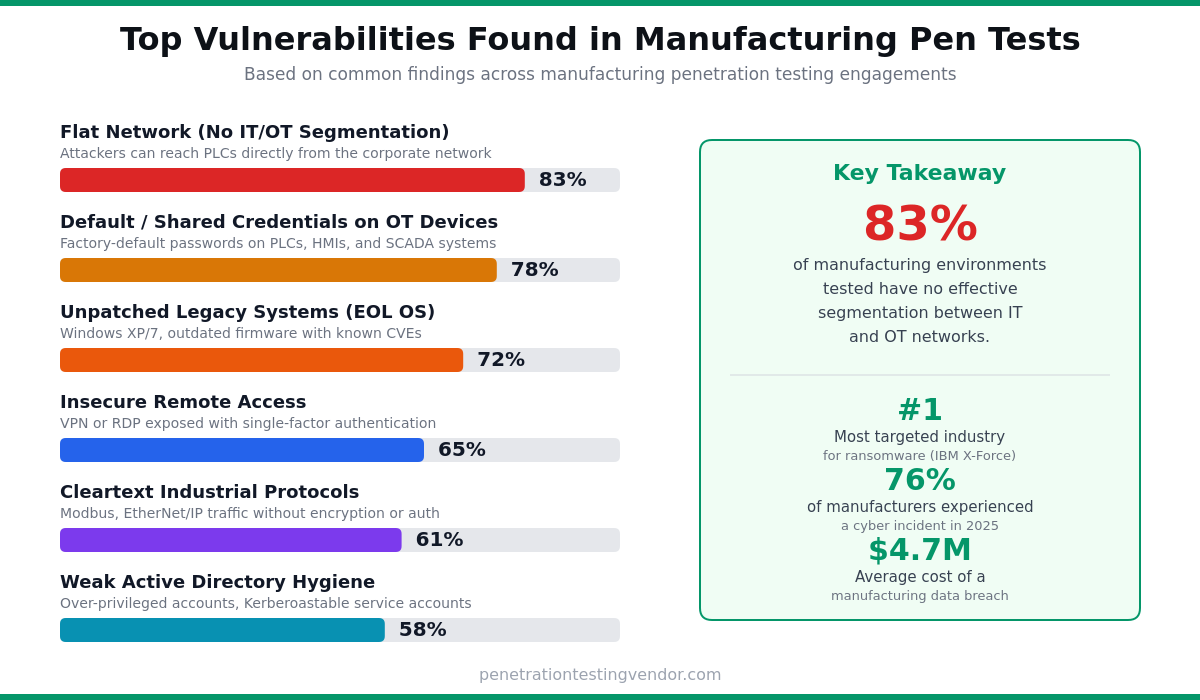
Penetration testers consistently find a pattern of vulnerabilities across manufacturing clients. Understanding these common findings can help organizations prioritize their security efforts even before engaging a testing firm.
Flat network architecture is perhaps the most dangerous and prevalent issue. Many manufacturing facilities have minimal or no segmentation between the corporate network and the production floor. An attacker who compromises a workstation in the accounting department can scan the network and discover PLCs, HMIs, and SCADA servers directly. Proper segmentation using the Purdue Model or IEC 62443 zones and conduits architecture is essential, yet rarely implemented completely.
Default and shared credentials are endemic in OT environments. PLCs and HMIs frequently ship with well-known default passwords, and changing them can be operationally complex because it may require coordinating maintenance windows. Testers often find that entire production lines share a single password, and that remote access solutions use easily guessable credentials. Combined with the lack of multi-factor authentication on OT systems, this creates straightforward paths to compromise.
Unpatched systems and legacy software represent another consistent finding. When a PLC runs firmware from 2012 or an HMI operates on Windows 7, there is no realistic path to patching these systems in the traditional sense. Penetration testing helps identify which of these legacy systems are actually exposed and reachable from the network, allowing organizations to implement compensating controls such as network segmentation, application whitelisting, or virtual patching through IDS/IPS rules.
Insecure remote access has become even more prevalent since the shift toward remote operations. Many manufacturers deployed VPN or remote desktop solutions quickly to enable remote monitoring and maintenance, without implementing proper access controls. Testers frequently find remote access portals exposed to the internet with single-factor authentication, providing a direct path into industrial control networks.
Safety Considerations During OT Penetration Testing
Testing in a manufacturing environment carries risks that do not exist in standard IT penetration testing. Sending unexpected commands to a PLC could cause a robotic arm to move unexpectedly, a chemical process to destabilize, or a conveyor system to malfunction. For this reason, OT penetration testing requires specialized expertise and careful planning.
Reputable testing firms will work with plant engineers and operations teams to define clear rules of engagement. Testing against active production systems should be limited to passive reconnaissance and network analysis during normal operations. Active exploitation testing against OT devices should be conducted during scheduled maintenance windows or, ideally, in a staging environment that mirrors the production setup. The scoping process for a manufacturing pen test is more involved than a standard engagement, and it should always include input from both IT security and plant operations teams.
Some testing approaches minimize risk while still providing valuable findings. Network traffic analysis can reveal insecure protocols and unauthorized connections without sending any packets to OT devices. Configuration reviews of firewalls, switches, and segmentation controls identify weaknesses in the architecture without touching production equipment. And testing the IT-to-OT pivot path from the corporate network can demonstrate whether an attacker could reach the production floor, stopping short of actually interacting with controllers.
Compliance Drivers for Manufacturing Penetration Testing
Several regulatory and industry frameworks increasingly require or strongly recommend penetration testing for manufacturers. Organizations in the defense industrial base must comply with CMMC 2.0 requirements, which include security assessment practices that encompass penetration testing for organizations handling Controlled Unclassified Information (CUI).
IEC 62443, the international standard for industrial automation and control system security, defines security levels and zones that can be validated through penetration testing. Many manufacturers pursuing IEC 62443 certification use pen testing to verify that their zone and conduit architecture effectively contains threats.
NIST SP 800-82, the guide to industrial control systems security, recommends regular security assessments including penetration testing as part of a comprehensive ICS security program. The NIST Cybersecurity Framework (CSF), widely adopted by manufacturers, also includes assessment activities that align with penetration testing practices.
For manufacturers that process payment card data through point-of-sale systems in retail operations or customer portals, PCI DSS requirements mandate regular penetration testing. And organizations with operations in the European Union must consider GDPR implications when employee or customer personal data could be exposed through a breach of manufacturing systems.
Building a Manufacturing Penetration Testing Program
Rather than treating penetration testing as a one-time checkbox exercise, manufacturers should build an ongoing testing program that matures over time. A practical approach starts with an initial assessment focused on the IT-OT boundary, since this is where the highest-risk vulnerabilities tend to cluster.
During the first engagement, the testing team should map the entire network architecture, identify all IT-to-OT pathways, and test the effectiveness of segmentation controls. This baseline assessment often reveals critical issues like flat networks, exposed remote access, and default credentials that can be remediated before subsequent tests dive deeper.
Follow-up engagements can then expand scope to include specific OT components, social engineering against plant personnel, physical security testing of production facilities, and wireless network assessments of the shop floor. Many manufacturers operate multiple facilities, each with its own network architecture and equipment, so a phased approach that tests different sites over time provides comprehensive coverage without overwhelming the security team.
Annual penetration testing should be the minimum frequency, with additional testing triggered by significant changes such as new IIoT deployments, network architecture modifications, mergers or acquisitions of new facilities, or the deployment of new manufacturing execution systems (MES). Continuous penetration testing models are particularly well-suited to manufacturing because the attack surface changes frequently as new equipment is commissioned and decommissioned.
What to Look for in a Manufacturing Penetration Testing Vendor
Not every penetration testing firm is qualified to test manufacturing environments. OT penetration testing requires specialized knowledge of industrial protocols, safety-critical systems, and the operational constraints of production environments. When evaluating vendors, look for teams with specific ICS/SCADA testing experience, relevant certifications such as GICSP (Global Industrial Cyber Security Professional), and a demonstrable understanding of the Purdue Model and IEC 62443 frameworks.
The vendor should be willing to work collaboratively with your plant operations team, not just your IT department. They should have a clear methodology for avoiding disruption to production systems, including defined escalation procedures if unexpected behavior is observed during testing. Ask for references from other manufacturing clients, and ensure the final report includes both executive-level risk summaries and technical remediation guidance specific to industrial environments.
The deliverables should go beyond a list of vulnerabilities. A high-quality manufacturing pen test report maps attack paths from initial entry to production impact, quantifies risk in terms the business understands (downtime cost, safety implications, supply chain disruption), and provides a prioritized remediation roadmap that accounts for the operational constraints of patching and reconfiguring OT systems.
Getting Started
Manufacturing cybersecurity is no longer optional. The combination of increasing connectivity, persistent threat actor interest, and tightening regulatory requirements means that every manufacturer needs to understand their security posture. Penetration testing provides the most realistic assessment of how an attacker would actually compromise your environment, from the initial phishing email or exposed VPN portal all the way to the production floor.
If your organization has never conducted a penetration test that includes OT systems, start with a scoping conversation that includes both IT and plant operations stakeholders. Define what systems are in scope, establish safety boundaries, and choose a testing partner with genuine manufacturing experience. The findings will almost certainly justify the investment, and the remediation roadmap will give you a clear path toward securing your most critical operational assets.
